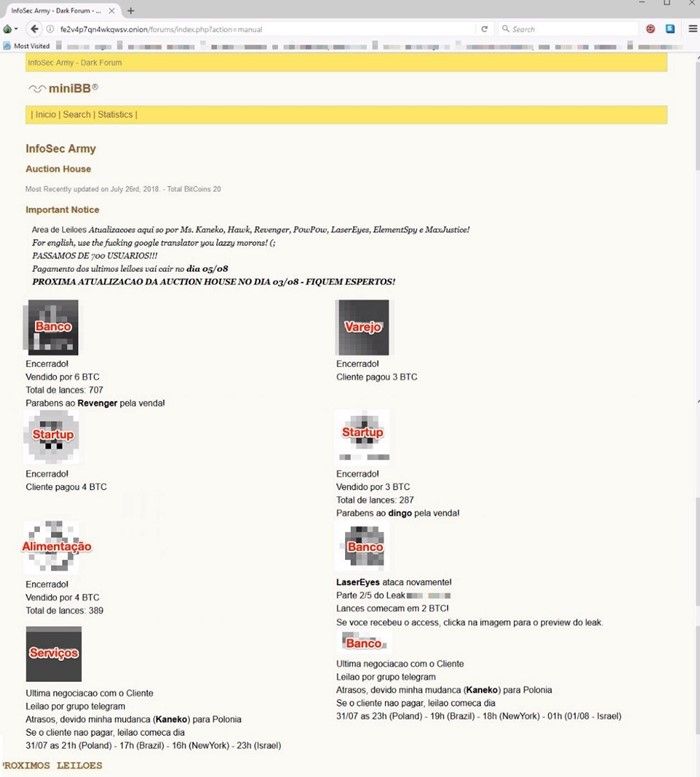
Brazilian security firm Tempest has investigated recent darkweb auction-rooms of so-called “InfoSec Army.” The data sold was extracted from various Brazilian corporations, financial groups, and small businesses. Tempest estimated a total profit of $320 thousand in bitcoins by the end of August 2018:
“Some databases would have been sold on the InfoSec Army in trading sessions with more than 700 bids and the most valuable base would have been sold for six bitcoins. The forum contained the date and time of the trading sessions and information about each of the items for sale. Already the reverse auction happened Telegram froups.
The InfoSec Army page was taken off the air in August 2018; however, among the data for sale were users and passwords, administrative access to attacked environments, copies of documents, source codes, emails, images, and even complete databases. These archives can be combined with several others and used in different scams like opening accounts, extortion, or performing fraudulent transactions.
Vendors gave detailed descriptions of the ways they used to steal the data. Some evidence and samples were also offered so that buyers could validate the data.
In one case, the attacker says he bought access to a control panel with more than 2000 zombie computers. Investigating these computers, he arrived at the workstation of an employee of one of the companies that had the data stolen. From this station the attacker was able to move around the network, identify outdated systems and obtain administrative access to the domain controller, from where it was possible to access any computer on the network,” declared Tempest.
Although Brazil has been taking significant steps in the right direction in regards to cybersecurity, such attacks persist in Brazil. A 2017 study from Norton Cyber Security indicated that Brazil is the second highest cyberattacked country, affecting 62 million people, and costing $22 billion. Coincidentally, the data auction took place just a few weeks after The Brazilian Army’s Cyber Defense Command executed an unprecedented military and civilian exercise at Fort Marechal Rondon, Brazil, between July the 3rd and 6th, 2018. However, the markets are hopeful that the new president-elect Jair Bolsonaro will maintain his strong anti-corruption beliefs in hopes of cleaning the internet of crime as well.
SOURCE:
https://www.scriptbrasil.com.br/vida-digital/hackers-leiloando-dados-deep-web.html
https://dialogo-americas.com/en/articles/brazilian-army-conducts-unprecedented-cyberdefense-exercise